In cryptography, a salt is random data fed as an additional input to a one-way function that hashes data, a password or passphrase. Salting helps defend... 13 KB (1,481 words) - 10:58, 19 December 2023 |
In cryptography, a pepper is a secret added to an input such as a password during hashing with a cryptographic hash function. This value differs from... 8 KB (1,061 words) - 19:58, 10 October 2023 |
 | In cryptography, a nonce is an arbitrary number that can be used just once in a cryptographic communication. It is often a random or pseudo-random number... 7 KB (898 words) - 00:40, 15 April 2024 |
In cryptography, padding is any of a number of distinct practices which all include adding data to the beginning, middle, or end of a message prior to... 23 KB (3,307 words) - 18:11, 14 February 2024 |
reasons Salt (cryptography), a method to secure passwords Salted bomb, a nuclear weapon specifically engineered to enhance residual radioactivity Salting (confidence... 2 KB (274 words) - 22:53, 27 March 2024 |
the album So Numb "Salt", a mini-opera for alto voice, amplified cello and electronics by Missy Mazzoli from 2012 Salt (cryptography), random data that... 8 KB (985 words) - 14:59, 11 March 2024 |
cryptographically secure pseudorandom number generator or from a hardware random number generator. Salt (cryptography) Pseudorandomness Cryptographic... 2 KB (242 words) - 15:53, 27 December 2023 |
Preimage attack (category Cryptographic attacks) In cryptography, a preimage attack on cryptographic hash functions tries to find a message that has a specific hash value. A cryptographic hash function... 7 KB (895 words) - 15:44, 13 April 2024 |
A key in cryptography is a piece of information, usually a string of numbers or letters that are stored in a file, which, when processed through a cryptographic... 12 KB (1,496 words) - 14:16, 25 March 2024 |
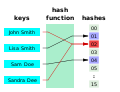
 | A cryptographic hash function (CHF) is a hash algorithm (a map of an arbitrary binary string to a binary string with a fixed size of n {\displaystyle... 45 KB (6,067 words) - 11:48, 27 April 2024 |
PBKDF2 (category Cryptography standards) passphrase along with a salt value and repeats the process many times to produce a derived key, which can then be used as a cryptographic key in subsequent... 13 KB (1,341 words) - 09:19, 24 February 2024 |
and topical guide to cryptography: Cryptography (or cryptology) – practice and study of hiding information. Modern cryptography intersects the disciplines... 20 KB (1,876 words) - 10:47, 24 February 2024 |
competition Cryptographic nonce Salt (cryptography) Cryptographic strength Block cipher Block cipher mode of operation Stream cipher Key (cryptography) Key size... 19 KB (1,792 words) - 12:20, 28 December 2023 |
Initialization vector (category Cryptography) In cryptography, an initialization vector (IV) or starting variable is an input to a cryptographic primitive being used to provide the initial state.... 14 KB (1,779 words) - 08:47, 29 April 2024 |
 | In cryptography, a key derivation function (KDF) is a cryptographic algorithm that derives one or more secret keys from a secret value such as a master... 13 KB (1,625 words) - 17:56, 8 March 2024 |
Crypt (C) (category Broken cryptography algorithms) the newer directory services (ds) system. Key derivation function Salt (cryptography) crypt(3) – FreeBSD Library Functions Manual Simson Garfinkel, Alan... 28 KB (3,030 words) - 14:45, 23 April 2024 |
NaCl (software) (category Cryptographic software) NaCl (Networking and Cryptography Library, pronounced "salt") is a public domain, high-speed software library for cryptography. NaCl was created by the... 9 KB (722 words) - 05:13, 26 March 2024 |
Password Hashing Competition (redirect from Makwa (cryptography)) hash function competition Password Hashing Competition Utilization Hash-based cryptography Merkle tree Message authentication Proof of work Salt Pepper... 3 KB (254 words) - 01:08, 11 October 2023 |
Articles related to cryptography include: A5/1 • A5/2 • ABA digital signature guidelines • ABC (stream cipher) • Abraham Sinkov • Acoustic cryptanalysis... 67 KB (2,943 words) - 23:51, 25 November 2023 |
Message authentication code (redirect from MAC (cryptography)) In cryptography, a message authentication code (MAC), sometimes known as an authentication tag, is a short piece of information used for authenticating... 15 KB (1,781 words) - 08:44, 18 April 2024 |
Convergent encryption (category Cryptography) encryption), or to simply not use convergent encryption in the first place. Salt (cryptography) Deterministic encryption Secure Data Deduplication, Mark W. Storer... 5 KB (797 words) - 16:13, 26 January 2023 |
 | Introducing the new caching framework Security improvements with Salt (cryptography) & RSA Integration of Extbase & Fluid features Current version: 4... 36 KB (2,549 words) - 08:26, 24 April 2024 |
Challenge–response authentication (redirect from Challenge (Cryptography)) impractical to implement a true nonce, a strong cryptographically secure pseudorandom number generator and cryptographic hash function can generate challenges that... 11 KB (1,560 words) - 00:27, 19 January 2024 |
HKDF (category Cryptography) shared secret generated using Diffie-Hellman, and an optional salt, and generates a cryptographic key called the PRK ("pseudorandom key"). This acts as a "randomness... 6 KB (693 words) - 17:48, 29 October 2023 |
In cryptography, cryptographic hash functions can be divided into two main categories. In the first category are those functions whose designs are based... 13 KB (1,950 words) - 08:07, 27 April 2022 |
 | Hash collision (redirect from Cryptographic hash collision) collisions in data management and computer security (in particular, cryptographic hash functions), collision avoidance has become an important topic in... 12 KB (1,456 words) - 23:04, 28 February 2024 |
 | Avalanche effect (redirect from Avalanche (cryptography)) In cryptography, the avalanche effect is the desirable property of cryptographic algorithms, typically block ciphers and cryptographic hash functions... 5 KB (568 words) - 17:23, 14 December 2023 |
Rainbow table (category Cryptographic attacks) A rainbow table is a precomputed table for caching the outputs of a cryptographic hash function, usually for cracking password hashes. Passwords are typically... 24 KB (3,456 words) - 20:43, 21 April 2024 |
Panama is a cryptographic primitive which can be used both as a hash function and a stream cipher, but its hash function mode of operation has been broken... 4 KB (350 words) - 00:49, 27 September 2023 |

