The Secure Hash Algorithms are a family of cryptographic hash functions published by the National Institute of Standards and Technology (NIST) as a U...
3 KB (464 words) - 07:05, 4 October 2024
A cryptographic hash function (CHF) is a hash algorithm (a map of an arbitrary binary string to a binary string with a fixed size of n {\displaystyle...
49 KB (6,299 words) - 15:10, 30 May 2025
from a hash function which takes a data input and returns a fixed length of bits. Although hash algorithms, especially cryptographic hash algorithms, have...
9 KB (1,142 words) - 20:01, 19 June 2025
SHA-3 hash algorithm. The winning hash function has been published as NIST FIPS 202 the "SHA-3 Standard", to complement FIPS 180-4, the Secure Hash Standard...
27 KB (2,244 words) - 07:44, 6 June 2025
Hash-based cryptography is the generic term for constructions of cryptographic primitives based on the security of hash functions. It is of interest as...
20 KB (2,329 words) - 03:24, 18 June 2025
SHA-2 (category Cryptographic hash functions)
SHA-2 (Secure Hash Algorithm 2) is a set of cryptographic hash functions designed by the United States National Security Agency (NSA) and first published...
52 KB (4,982 words) - 14:44, 24 May 2025
Message authentication code (redirect from Keyed hash function)
cryptographic hash functions (as in the case of HMAC) or from block cipher algorithms (OMAC, CCM, GCM, and PMAC). However many of the fastest MAC algorithms, like...
16 KB (1,918 words) - 17:55, 22 January 2025
as a secure message authentication code (MAC). SipHash, however, is not a general purpose key-less hash function such as Secure Hash Algorithms (SHA)...
14 KB (1,342 words) - 17:18, 17 February 2025
theory and formal reduction. These functions are called provably secure cryptographic hash functions. To construct these is very difficult, and few examples...
14 KB (1,823 words) - 18:28, 7 January 2025
a checksum. Hash function security summary Secure Hash Algorithms NIST hash function competition Key derivation functions (category) "Hash functions"....
10 KB (279 words) - 12:52, 24 May 2025
HMAC (redirect from Keyed-Hashing Message Authentication)
requires |journal= (help) Eastlake, 3rd, D.; Hansen, T. (May 2011). US Secure Hash Algorithms (SHA and SHA-based HMAC and HKDF). Internet Engineering Task Force...
18 KB (2,316 words) - 18:51, 16 April 2025
The MD2 Message-Digest Algorithm is a cryptographic hash function developed by Ronald Rivest in 1989. The algorithm is optimized for 8-bit computers. MD2...
9 KB (1,053 words) - 04:19, 31 December 2024
SHA-3 (category Cryptographic hash functions)
SHA-3 (Secure Hash Algorithm 3) is the latest member of the Secure Hash Algorithm family of standards, released by NIST on August 5, 2015. Although part...
52 KB (5,726 words) - 19:03, 2 June 2025
Cryptography (section Cryptographic hash functions)
bare digest algorithms, and so has been thought worth the effort. Cryptographic hash functions are a third type of cryptographic algorithm. They take a...
99 KB (11,007 words) - 11:28, 7 June 2025
Key derivation function (redirect from Password hash)
illustrated the importance of algorithm selection in securing passwords. Although bcrypt was employed to protect the hashes (making large scale brute-force...
13 KB (1,640 words) - 18:48, 30 April 2025
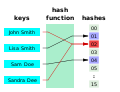
output. The values returned by a hash function are called hash values, hash codes, (hash/message) digests, or simply hashes. The values are usually used to...
50 KB (7,455 words) - 21:00, 27 May 2025
SHA-1 (redirect from SHA-1 hash)
In cryptography, SHA-1 (Secure Hash Algorithm 1) is a hash function which takes an input and produces a 160-bit (20-byte) hash value known as a message...
50 KB (5,744 words) - 14:18, 17 March 2025
Length extension attack (redirect from Hash length extension attack)
information at the end of the message and produce a valid hash without knowing the secret. Algorithms like MD5, SHA-1 and most of SHA-2 that are based on the...
8 KB (1,082 words) - 12:51, 23 April 2025
follows these steps: Calculate e = HASH ( m ) {\displaystyle e={\textrm {HASH}}(m)} . (Here HASH is a cryptographic hash function, such as SHA-2, with the...
19 KB (2,833 words) - 08:53, 8 May 2025
Skein Hash Function Family" (PDF). Archived from the original (PDF) on 2014-08-24. Retrieved 2010-12-15. "NIST Selects Winner of Secure Hash Algorithm (SHA-3)...
9 KB (822 words) - 12:52, 13 April 2025
The Commercial National Security Algorithm Suite (CNSA) is a set of cryptographic algorithms promulgated by the National Security Agency as a replacement...
10 KB (655 words) - 21:48, 19 June 2025
TrueCrypt) included Whirlpool (the final version) as one of its supported hash algorithms. Digital timestamping Florian Mendel1, Christian Rechberger, Martin...
11 KB (1,054 words) - 03:57, 19 March 2024
increased to 16. Throughout the NIST hash function competition, entrants are permitted to "tweak" their algorithms to address issues that are discovered...
31 KB (2,888 words) - 17:05, 21 May 2025
Symmetric-key algorithms are algorithms for cryptography that use the same cryptographic keys for both the encryption of plaintext and the decryption...
15 KB (1,540 words) - 21:14, 19 June 2025
Merkle tree (redirect from Tiger-Tree Hash)
cryptographic hash of the labels of its child nodes. A hash tree allows efficient and secure verification of the contents of a large data structure. A hash tree...
15 KB (1,822 words) - 16:33, 18 June 2025
Salt (cryptography) (redirect from Salted hash)
salt is random data fed as an additional input to a one-way function that hashes data, a password or passphrase. Salting helps defend against attacks that...
13 KB (1,527 words) - 22:35, 14 June 2025
the hash ratchet HMAC. The following is a list of applications that use the Double Ratchet Algorithm or a custom implementation of it: ChatSecure Conversations...
15 KB (1,391 words) - 09:37, 22 April 2025
through the idea of "reusable proof of work" using the 160-bit secure hash algorithm 1 (SHA-1). Proof of work was later popularized by Bitcoin as a foundation...
37 KB (4,073 words) - 04:05, 16 June 2025
In cryptography, N-hash is a cryptographic hash function based on the FEAL round function, and is now considered insecure. It was proposed in 1990 in an...
2 KB (213 words) - 21:43, 31 December 2023