Computer security compromised by hardware failure is a branch of computer security applied to hardware. The objective of computer security includes protection...
41 KB (5,114 words) - 00:21, 21 January 2024
digital computer and communication systems and networks NEI 08-09: Cybersecurity Plan for Nuclear Power Plants Computer security compromised by hardware failure...
6 KB (609 words) - 16:51, 26 March 2025
In computer security, a sandbox is a security mechanism for separating running programs, usually in an effort to mitigate system failures and/or software...
10 KB (1,000 words) - 12:32, 12 November 2024
In computer security, a threat is a potential negative action or event enabled by a vulnerability that results in an unwanted impact to a computer system...
39 KB (4,709 words) - 04:18, 5 May 2025
Concept to reduce computer security risks Fault tolerance – Resilience of systems to component failures or errors Hardware security – Security architecture...
220 KB (22,338 words) - 20:40, 28 April 2025
be exploited by a malicious actor to compromise its security. Despite intentions to achieve complete correctness, virtually all hardware and software...
26 KB (3,290 words) - 21:09, 28 April 2025
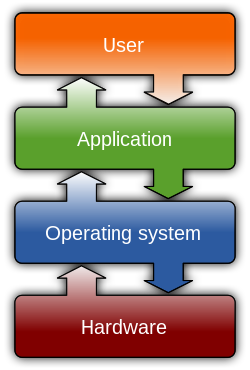
Operating system (redirect from Computer operating sysem)
is system software that manages computer hardware and software resources, and provides common services for computer programs. Time-sharing operating...
70 KB (8,176 words) - 17:11, 7 May 2025
enable real-time analysis of security alerts generated by applications and network hardware. SIEM systems are central to security operations centers (SOCs)...
28 KB (3,089 words) - 11:16, 11 April 2025
caused by failing or disconnected hardware or software. In this context, the cascading failure is known by the term cascade failure. A cascade failure can...
23 KB (2,953 words) - 22:30, 28 April 2025
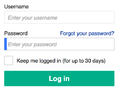
Multi-factor authentication (category Computer access control)
significantly less likely to be compromised. Authentication takes place when someone tries to log into a computer resource (such as a computer network, device, or...
43 KB (4,725 words) - 15:33, 5 May 2025
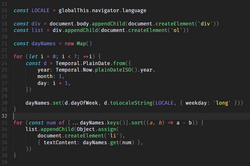
Software (redirect from Computer Software)
development of digital computers in the mid-20th century. Early programs were written in the machine language specific to the hardware. The introduction of...
26 KB (3,067 words) - 11:05, 24 April 2025
Kerckhoffs's principle (redirect from Security through transparency)
cryptographic algorithm may be implemented by hardware and software that is widely distributed among users. If security depends on keeping that secret, then...
15 KB (1,720 words) - 12:42, 1 May 2025
Rootkit (redirect from Hardware rootkit)
password-stealing key loggers and computer viruses. Appropriate the compromised machine as a zombie computer for attacks on other computers. (The attack originates...
69 KB (7,095 words) - 09:41, 7 March 2025
Data recovery (redirect from Data recovery hardware)
scenario involves a drive-level failure, such as a compromised file system or drive partition, or a hard disk drive failure. In any of these cases, the data...
30 KB (3,625 words) - 21:59, 18 April 2025
Wake-on-LAN (category Computer-related introductions in 1997)
an Ethernet or Token Ring computer networking standard that allows a computer to be turned on or awakened from sleep mode by a network message. The message...
33 KB (4,307 words) - 18:49, 28 April 2025
to a local computer over a network from a central server. Images do not have to support specific hardware configurations and the security settings can...
123 KB (11,994 words) - 10:44, 26 April 2025
Legacy system (redirect from Legacy hardware)
need of replacement. Legacy code is old computer source code that is no longer supported on standard hardware and environments, and is a codebase that...
25 KB (3,138 words) - 09:08, 3 January 2025
Data erasure (redirect from Computer and electronic data destruction)
improperly disposed computer. Oklahoma Corporation Commission (2008-05-21): Server sold at auction compromises more than 5,000 Social Security numbers. Department...
31 KB (3,085 words) - 19:58, 4 January 2025
Password (redirect from Computer password)
as hardware tokens and biometric security. Password rotation is a policy that is commonly implemented with the goal of enhancing computer security. In...
79 KB (9,039 words) - 13:23, 5 May 2025
Wi-Fi Protected Access (redirect from WPA security)
3 (WPA3) are the three security certification programs developed after 2000 by the Wi-Fi Alliance to secure wireless computer networks. The Alliance defined...
40 KB (4,663 words) - 08:23, 8 May 2025
Cyberwarfare (redirect from Cyber security attack)
"Farewell Dossier" provided information on this attack, and wrote that compromised computer chips would become a part of Soviet military equipment, flawed turbines...
150 KB (16,063 words) - 03:31, 6 May 2025
RAID (redirect from Hardware RAID compared to Software RAID)
on performance by an array of the inexpensive drives that had been developed for the growing personal computer market. Although failures would rise in...
61 KB (7,162 words) - 20:47, 19 March 2025
technology (IT) security specialists. These specialists apply information security to technology (most often some form of computer system). IT security specialists...
159 KB (18,159 words) - 22:30, 4 May 2025
Byzantine fault (redirect from Byzantine failure)
agreement problem, or a Byzantine failure. Byzantine fault tolerance (BFT) is the resilience of a fault-tolerant computer system or similar system to such...
34 KB (4,058 words) - 16:43, 22 February 2025
Kernel (operating system) (redirect from Kernel (computer))
kernel security. They propose their driver isolation framework for protection, primarily in the Linux kernel. Typical computer systems today use hardware-enforced...
82 KB (10,151 words) - 18:56, 5 May 2025
Embedded system (redirect from Embedded hardware)
An embedded system is a specialized computer system—a combination of a computer processor, computer memory, and input/output peripheral devices—that has...
42 KB (5,298 words) - 14:11, 7 April 2025
Thin client (redirect from Network computer)
of centralization are hardware resource optimization, reduced software maintenance, and improved security. Example of hardware resource optimization:...
16 KB (2,075 words) - 08:18, 9 March 2025
life-changing influences. Physical security is needed to protect the value of the hardware therein. The cost of a breach of security can have severe consequences...
22 KB (2,702 words) - 20:55, 15 January 2024
Asus (redirect from ASUSTeK Computer)
ASUSTeK Computer Inc. (/ˈeɪsuːs/, /eɪˈsuːs/, /ɑːˈ-/, /əˈ-/; stylized as ASUSTeK or ASUS) is a Taiwanese multinational computer, phone hardware and electronics...
73 KB (6,587 words) - 21:08, 4 May 2025
Operational technology (section Security)
one network can potentially be exploited to compromise the other. Supply chain risks: Compromised hardware or software components in the OT network can...
15 KB (1,866 words) - 13:44, 30 April 2025