MD2 Message-Digest Algorithm is a cryptographic hash function developed by Ronald Rivest in 1989. The algorithm is optimized for 8-bit computers. MD2...
9 KB (1,053 words) - 04:19, 31 December 2024
MD2 or MD-2 may refer to: MD2 (file format) MD2 (hash function) MD-2 (immunology) MD2 low-profile PCI card IMBEL MD2 Rifle Maryland's 2nd congressional...
316 bytes (68 words) - 12:24, 29 December 2023
checksum. Hash function security summary Secure Hash Algorithms NIST hash function competition Key derivation functions (category) "Hash functions". www.azillionmonkeys...
10 KB (279 words) - 12:52, 24 May 2025
BLAKE is a cryptographic hash function based on Daniel J. Bernstein's ChaCha stream cipher, but a permuted copy of the input block, XORed with round constants...
31 KB (2,888 words) - 17:05, 21 May 2025
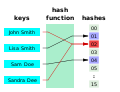
derived from a hash function which takes a data input and returns a fixed length of bits. Although hash algorithms, especially cryptographic hash algorithms...
9 KB (1,142 words) - 00:48, 10 June 2025
A cryptographic hash function (CHF) is a hash algorithm (a map of an arbitrary binary string to a binary string with a fixed size of n {\displaystyle...
49 KB (6,299 words) - 15:10, 30 May 2025
In cryptography, N-hash is a cryptographic hash function based on the FEAL round function, and is now considered insecure. It was proposed in 1990 in an...
2 KB (213 words) - 21:43, 31 December 2023
to a spate of "hash flooding" denial-of-service attacks (HashDoS) in late 2011. SipHash is designed as a secure pseudorandom function and can also be...
14 KB (1,342 words) - 17:18, 17 February 2025
cryptography, Whirlpool (sometimes styled WHIRLPOOL) is a cryptographic hash function. It was designed by Vincent Rijmen (co-creator of the Advanced Encryption...
11 KB (1,054 words) - 03:57, 19 March 2024
contest could not be won even with completely broken algorithms such as MD2 (hash function) used as key stream extractor, and primitives such as the Dual EC...
215 KB (19,289 words) - 14:32, 15 June 2025
cryptographic hash functions. Note that not all entries may be up to date. For a summary of other hash function parameters, see comparison of cryptographic hash functions...
17 KB (1,063 words) - 06:46, 25 May 2025
HMAC (redirect from Keyed-Hashing Message Authentication)
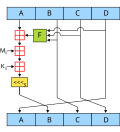
type of message authentication code (MAC) involving a cryptographic hash function and a secret cryptographic key. As with any MAC, it may be used to simultaneously...
18 KB (2,316 words) - 18:51, 16 April 2025
LSH is a cryptographic hash function designed in 2014 by South Korea to provide integrity in general-purpose software environments such as PCs and smart...
44 KB (3,102 words) - 23:16, 20 July 2024
Merkle tree (redirect from Tiger-Tree Hash)
the above picture hash 0 is the result of hashing the concatenation of hash 0-0 and hash 0-1. That is, hash 0 = hash( hash 0-0 + hash 0-1 ) where "+" denotes...
15 KB (1,804 words) - 11:52, 27 May 2025
SIMD is a cryptographic hash function based on the Merkle–Damgård construction submitted to the NIST hash function competition by Gaëtan Leurent. It is...
1 KB (127 words) - 13:39, 9 February 2023
The Secure Hash Algorithms are a family of cryptographic hash functions published by the National Institute of Standards and Technology (NIST) as a U.S...
3 KB (464 words) - 07:05, 4 October 2024
JH is a cryptographic hash function submitted to the NIST hash function competition by Hongjun Wu. Though chosen as one of the five finalists of the competition...
4 KB (399 words) - 17:35, 7 January 2025
The GOST hash function, defined in the standards GOST R 34.11-94 and GOST 34.311-95 is a 256-bit cryptographic hash function. It was initially defined...
16 KB (2,206 words) - 02:44, 11 July 2024
Skein is a cryptographic hash function and one of five finalists in the NIST hash function competition. Entered as a candidate to become the SHA-3 standard...
9 KB (822 words) - 12:52, 13 April 2025
Salt (cryptography) (redirect from Salted hash)
cryptography, a salt is random data fed as an additional input to a one-way function that hashes data, a password or passphrase. Salting helps defend against attacks...
13 KB (1,527 words) - 22:35, 14 June 2025
cryptographic primitives, including cryptographic hashes, message authentication codes, mask generation functions, stream ciphers, pseudo-random number generators...
7 KB (846 words) - 09:04, 19 April 2025
Preimage attack (redirect from Hash function preimage)
attack on cryptographic hash functions tries to find a message that has a specific hash value. A cryptographic hash function should resist attacks on...
7 KB (895 words) - 15:44, 13 April 2024
Fugue is a cryptographic hash function submitted by IBM to the NIST hash function competition. It was designed by Shai Halevi, William E. Hall, and Charanjit...
3 KB (651 words) - 10:35, 27 March 2025
ShangMi 3 (SM3) is a cryptographic hash function, standardised for use in commercial cryptography in China. It was published by the National Cryptography...
4 KB (335 words) - 01:57, 15 December 2024
multi-block-length hash function based on block ciphers" and typically achieves (asymptotic) rates between 1 and 2 independent of the hash size (only with...
24 KB (3,977 words) - 11:37, 24 March 2025
Yescrypt (category Cryptographic hash functions)
cryptographic key derivation function function used for password hashing on Fedora Linux, Debian, Ubuntu, and Arch Linux. The function is more resistant to offline...
2 KB (106 words) - 18:17, 31 March 2025
SHA-1 (redirect from SHA-1 hash)
SHA-1 function. In cryptography, SHA-1 (Secure Hash Algorithm 1) is a hash function which takes an input and produces a 160-bit (20-byte) hash value known...
50 KB (5,744 words) - 14:18, 17 March 2025
Rainbow table (redirect from Reduction function)
cryptographic hash function, usually for cracking password hashes. Passwords are typically stored not in plain text form, but as hash values. If such...
24 KB (3,485 words) - 14:46, 6 June 2025