In cryptography, cryptographic hash functions can be divided into two main categories. In the first category are those functions whose designs are based...
14 KB (1,823 words) - 18:28, 7 January 2025
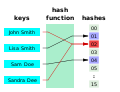
A cryptographic hash function (CHF) is a hash algorithm (a map of an arbitrary binary string to a binary string with a fixed size of n {\displaystyle n}...
49 KB (6,299 words) - 15:10, 30 May 2025
general and technical information for a number of cryptographic hash functions. See the individual functions' articles for further information. This article...
16 KB (806 words) - 04:43, 24 May 2025
This is a list of hash functions, including cyclic redundancy checks, checksum functions, and cryptographic hash functions. Adler-32 is often mistaken...
10 KB (279 words) - 12:52, 24 May 2025
The non-cryptographic hash functions (NCHFs) are hash functions intended for applications that do not need the rigorous security requirements of the cryptographic...
7 KB (796 words) - 00:45, 28 April 2025
In cryptography, security level is a measure of the strength that a cryptographic primitive — such as a cipher or hash function — achieves. Security level...
13 KB (1,332 words) - 01:56, 12 March 2025
Comparison of cryptographic hash functions Cryptographic hash function Collision attack Preimage attack Length extension attack Cipher security summary Tao...
17 KB (1,063 words) - 06:46, 25 May 2025
science and cryptography, Whirlpool (sometimes styled WHIRLPOOL) is a cryptographic hash function. It was designed by Vincent Rijmen (co-creator of the Advanced...
11 KB (1,054 words) - 03:57, 19 March 2024
The Secure Hash Algorithms are a family of cryptographic hash functions published by the National Institute of Standards and Technology (NIST) as a U...
3 KB (464 words) - 07:05, 4 October 2024
BLAKE is a cryptographic hash function based on Daniel J. Bernstein's ChaCha stream cipher, but a permuted copy of the input block, XORed with round constants...
31 KB (2,888 words) - 17:05, 21 May 2025
security (in particular, cryptographic hash functions), collision avoidance has become an important topic in computer security. Hash collisions can be unavoidable...
9 KB (1,142 words) - 20:01, 19 June 2025
computer security systems. These routines include, but are not limited to, one-way hash functions and encryption functions. When creating cryptographic systems...
6 KB (819 words) - 05:08, 24 March 2025
(SM3) is a cryptographic hash function, standardised for use in commercial cryptography in China. It was published by the National Cryptography Administration...
4 KB (335 words) - 01:57, 15 December 2024
Hash-based cryptography is the generic term for constructions of cryptographic primitives based on the security of hash functions. It is of interest as...
20 KB (2,329 words) - 03:24, 18 June 2025
function (which typically uses a cryptographic hash function or block cipher). KDFs can be used to stretch keys into longer keys or to obtain keys of...
13 KB (1,640 words) - 18:48, 30 April 2025
credentials to Internet security. Salts are related to cryptographic nonces. Without a salt, identical passwords will map to identical hash values, which could...
13 KB (1,527 words) - 22:35, 14 June 2025
The MD2 Message-Digest Algorithm is a cryptographic hash function developed by Ronald Rivest in 1989. The algorithm is optimized for 8-bit computers....
9 KB (1,053 words) - 04:19, 31 December 2024
SHA-1 (redirect from SHA-1 hash)
SHA-1 function. In cryptography, SHA-1 (Secure Hash Algorithm 1) is a hash function which takes an input and produces a 160-bit (20-byte) hash value known...
50 KB (5,744 words) - 14:18, 17 March 2025
which a cryptographic hash function is computed, and only the resulting hash is digitally signed. Cryptographic hash functions are functions that take...
100 KB (11,007 words) - 01:11, 20 June 2025
The Jenkins hash functions are a family of non-cryptographic hash functions for multi-byte keys designed by Bob Jenkins. The first one was formally published...
7 KB (852 words) - 21:39, 4 May 2024
HMAC (redirect from Keyed-Hashing Message Authentication)
code) is a specific type of message authentication code (MAC) involving a cryptographic hash function and a secret cryptographic key. As with any MAC, it...
18 KB (2,316 words) - 18:51, 16 April 2025
SHA-2 (category Cryptographic hash functions)
SHA-2 (Secure Hash Algorithm 2) is a set of cryptographic hash functions designed by the United States National Security Agency (NSA) and first published...
52 KB (4,982 words) - 02:56, 20 June 2025
Transport Layer Security (TLS) is a cryptographic protocol designed to provide communications security over a computer network, such as the Internet. The...
178 KB (17,519 words) - 23:52, 19 June 2025
cryptographic primitives, including cryptographic hashes, message authentication codes, mask generation functions, stream ciphers, pseudo-random number...
7 KB (846 words) - 09:04, 19 April 2025
Merkle tree (redirect from Tiger-Tree Hash)
In cryptography and computer science, a hash tree or Merkle tree is a tree in which every "leaf" node is labelled with the cryptographic hash of a data...
15 KB (1,822 words) - 16:33, 18 June 2025
filter (application for fast hashes) Cryptographic hash function Hash function Message authentication code List of hash functions Dobraunig, Christoph; Mendel...
14 KB (1,342 words) - 17:18, 17 February 2025
Collision attack (redirect from HashDoS)
In cryptography, a collision attack on a cryptographic hash tries to find two inputs producing the same hash value, i.e. a hash collision. This is in contrast...
17 KB (2,047 words) - 14:32, 21 June 2025
In cryptography, N-hash is a cryptographic hash function based on the FEAL round function, and is now considered insecure. It was proposed in 1990 in an...
2 KB (213 words) - 21:43, 31 December 2023
November 6, 2008. "cryptographic hash project – Background Information". Computer Security Resource Center. National Institute of Standards and Technology...
27 KB (2,244 words) - 07:44, 6 June 2025