Differential cryptanalysis is a general form of cryptanalysis applicable primarily to block ciphers, but also to stream ciphers and cryptographic hash...
13 KB (1,677 words) - 11:30, 9 March 2025
In cryptography, higher-order differential cryptanalysis is a generalization of differential cryptanalysis, an attack used against block ciphers. While...
5 KB (783 words) - 05:19, 26 August 2023
KN-Cipher (section Cryptanalysis)
secure against ordinary differential cryptanalysis, KN-Cipher was later broken using higher order differential cryptanalysis. Presented as "a prototype...
3 KB (200 words) - 05:46, 29 July 2025
In cryptography, truncated differential cryptanalysis is a generalization of differential cryptanalysis, an attack against block ciphers. Lars Knudsen...
4 KB (318 words) - 10:15, 4 January 2025
impossible differential cryptanalysis is a form of differential cryptanalysis for block ciphers. While ordinary differential cryptanalysis tracks differences...
10 KB (850 words) - 15:40, 7 December 2024
GOST (block cipher) (section Cryptanalysis of GOST)
Courtois; Michał Miształ (2011). "Differential Cryptanalysis of GOST". IACR. Nicolas T. Courtois (2012). "An Improved Differential Attack on Full GOST" (PDF)...
14 KB (1,469 words) - 19:58, 18 July 2025
Spectr-H64 (section Cryptanalysis)
Hong; Sangjin Lee & Jongin Lim (2003). "Linear Cryptanalysis on SPECTR-H64 with Higher Order Differential Property". Computer Network Security. Springer...
3 KB (282 words) - 08:59, 23 November 2023
PRESENT (section Cryptanalysis)
truncated differential attack on 26 out of 31 rounds of PRESENT was suggested in 2014. Several full-round attacks using biclique cryptanalysis have been...
7 KB (708 words) - 14:48, 26 January 2024
In cryptography, linear cryptanalysis is a general form of cryptanalysis based on finding affine approximations to the action of a cipher. Attacks have...
6 KB (812 words) - 13:20, 1 November 2023
XTEA (section Cryptanalysis)
Youngdai; Chang, Donghoon; Lee, Wonil; Lee, Sangjin (2004). "Differential Cryptanalysis of TEA and XTEA". In Lim, JI.; Lee, DH. (eds.). Information Security...
9 KB (969 words) - 14:09, 19 April 2025
Skipjack (cipher) (section Cryptanalysis)
exhaustive search) within months using impossible differential cryptanalysis. A truncated differential attack was also published against 28 rounds of Skipjack...
12 KB (1,134 words) - 16:36, 18 June 2025
Twofish (section Cryptanalysis)
is a truncated differential cryptanalysis of the full 16-round version. The paper claims that the probability of truncated differentials is 2−57.3 per...
9 KB (827 words) - 14:21, 3 April 2025
cryptography, mod n cryptanalysis is an attack applicable to block and stream ciphers. It is a form of partitioning cryptanalysis that exploits unevenness...
3 KB (412 words) - 17:18, 19 December 2024
Madryga (section Cryptanalysis)
non-linear component, and flaws in them are what both differential cryptanalysis and linear cryptanalysis seek to exploit. While Madryga's rotations are data-dependent...
5 KB (717 words) - 21:33, 16 March 2024
with less complexity than a brute-force search: differential cryptanalysis (DC), linear cryptanalysis (LC), and Davies' attack. However, the attacks are...
60 KB (6,704 words) - 20:26, 3 August 2025
Prince (cipher) (section Cryptanalysis)
cipher cryptanalysis" (PDF). {{cite journal}}: Cite journal requires |journal= (help) Posteuca, R.; Negara, G. (2015). "Integral cryptanalysis of round-reduced...
13 KB (1,376 words) - 13:37, 2 May 2024
XXTEA (section Cryptanalysis)
size of 212 bytes or more, and negligible work. It is based on differential cryptanalysis. To cipher "212 bytes or more" algorithm performs just 6 rounds...
9 KB (1,115 words) - 08:11, 28 June 2024
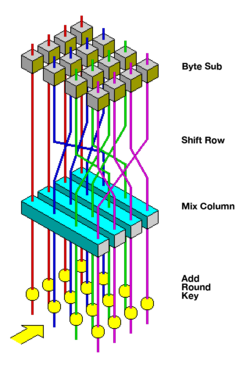
Block cipher (section Differential cryptanalysis)
growing catalog of attacks: truncated differential cryptanalysis, partial differential cryptanalysis, integral cryptanalysis, which encompasses square and integral...
51 KB (6,569 words) - 07:54, 3 August 2025
• CRHF • Crib (cryptanalysis) • Crowds (anonymity network) • Crypt (C) • Cryptanalysis • Cryptanalysis of the Enigma • Cryptanalysis of the Lorenz cipher...
66 KB (2,911 words) - 02:58, 27 July 2025
IDEA NXT). Unlike differential cryptanalysis, which uses pairs of chosen plaintexts with a fixed XOR difference, integral cryptanalysis uses sets or even...
8 KB (713 words) - 13:30, 10 July 2025
slices. This maximizes parallelism but also allows use of the extensive cryptanalysis work performed on DES. Serpent took a conservative approach to security...
16 KB (1,962 words) - 07:47, 17 April 2025
1994, the differential-linear attack is a mix of both linear cryptanalysis and differential cryptanalysis. The attack utilises a differential characteristic...
4 KB (385 words) - 03:30, 1 February 2024
M8 (cipher) (section Cryptanalysis)
cipher to a range of attacks, including differential cryptanalysis, linear cryptanalysis and mod n cryptanalysis. "ISO/IEC9979-0020 Register Entry" (PDF)...
8 KB (1,250 words) - 00:44, 31 August 2024
Speck (cipher) (section Cryptanalysis)
Speck in the standard attack model (CPA/CCA with unknown key) are differential cryptanalysis attacks; these make it through about 70–75% of the rounds of most...
23 KB (2,411 words) - 07:38, 25 May 2025
and Dmitry Khovratovich, Related-key Cryptanalysis of the Full AES-192 and AES-256, "Related-key Cryptanalysis of the Full AES-192 and AES-256". Table...
50 KB (5,679 words) - 04:23, 27 July 2025
perfect S-box. S-boxes can be analyzed using linear cryptanalysis and differential cryptanalysis in the form of a Linear approximation table (LAT) or...
10 KB (929 words) - 20:28, 24 May 2025
1999). It was found to be susceptible to an effective theoretical differential cryptanalysis attack considerably faster than an exhaustive search. LOKI Advanced...
4 KB (412 words) - 07:03, 27 April 2022
are not key-dependent, Khafre XORs subkeys every eight rounds. Differential cryptanalysis is effective against Khafre: 16 rounds can be broken using either...
9 KB (839 words) - 12:48, 9 June 2024
Boomerang attack (redirect from Amplified boomerang cryptanalysis)
the boomerang attack is a method for the cryptanalysis of block ciphers based on differential cryptanalysis. The attack was published in 1999 by David...
9 KB (864 words) - 04:16, 17 October 2023
Simon (cipher) (section Cryptanalysis)
was included to block slide and rotational cryptanalysis attacks.: 16 Still, rotational-XOR cryptanalysis has been used to find distinguishers against...
18 KB (1,841 words) - 22:50, 2 July 2025