In cryptography, encryption (more specifically, encoding) is the process of transforming information in a way that, ideally, only authorized parties can...
34 KB (3,645 words) - 17:52, 2 May 2025
Authenticated Encryption (AE) is an encryption scheme which simultaneously assures the data confidentiality (also known as privacy: the encrypted message...
19 KB (2,104 words) - 21:32, 28 April 2025
Symmetric-key algorithm (redirect from Symmetric encryption)
algorithms for cryptography that use the same cryptographic keys for both the encryption of plaintext and the decryption of ciphertext. The keys may be identical...
15 KB (1,540 words) - 19:12, 22 April 2025
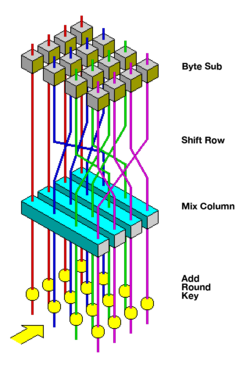
Advanced Encryption Standard (AES), also known by its original name Rijndael (Dutch pronunciation: [ˈrɛindaːl]), is a specification for the encryption of electronic...
50 KB (5,675 words) - 11:39, 17 March 2025
End-to-end encryption (E2EE) is a method of implementing a secure communication system where only communicating users can participate. No one else, including...
30 KB (3,142 words) - 20:08, 28 April 2025
Homomorphic encryption is a form of encryption that allows computations to be performed on encrypted data without first having to decrypt it. The resulting...
42 KB (4,692 words) - 23:00, 1 April 2025
Public-key cryptography (redirect from Asymmetric key encryption algorithm)
Diffie–Hellman key exchange, public-key key encapsulation, and public-key encryption. Public key algorithms are fundamental security primitives in modern cryptosystems...
40 KB (4,512 words) - 17:51, 26 March 2025
as cascade encryption, cascade ciphering, multiple encryption, and superencipherment. Superencryption refers to the outer-level encryption of a multiple...
9 KB (1,203 words) - 12:14, 19 March 2025
Probabilistic encryption is the use of randomness in an encryption algorithm, so that when encrypting the same message several times it will, in general...
4 KB (583 words) - 19:08, 11 February 2025
Block cipher mode of operation (redirect from Encryption mode)
itself is only suitable for the secure cryptographic transformation (encryption or decryption) of one fixed-length group of bits called a block. A mode...
52 KB (5,828 words) - 22:45, 25 April 2025
Structured encryption (STE) is a form of encryption that encrypts a data structure so that it can be privately queried. Structured encryption can be used...
4 KB (469 words) - 03:03, 22 March 2024
A deterministic encryption scheme (as opposed to a probabilistic encryption scheme) is a cryptosystem which always produces the same ciphertext for a...
7 KB (853 words) - 03:46, 23 September 2023
In cryptography and steganography, plausibly deniable encryption describes encryption techniques where the existence of an encrypted file or message is...
25 KB (2,867 words) - 02:15, 6 April 2025
Encryption software is software that uses cryptography to prevent unauthorized access to digital information. Cryptography is used to protect digital information...
10 KB (1,133 words) - 05:54, 19 April 2025
Pretty Good Privacy (redirect from Pgp encryption)
Pretty Good Privacy (PGP) is an encryption program that provides cryptographic privacy and authentication for data communication. PGP is used for signing...
56 KB (6,196 words) - 05:15, 7 April 2025
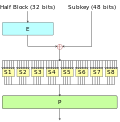
The Data Encryption Standard (DES /ˌdiːˌiːˈɛs, dɛz/) is a symmetric-key algorithm for the encryption of digital data. Although its short key length of...
60 KB (6,714 words) - 15:08, 11 April 2025
Disk encryption is a technology which protects information by converting it into code that cannot be deciphered easily by unauthorized people or processes...
17 KB (2,194 words) - 10:17, 19 March 2025
Transport Layer Security (redirect from Transport layer encryption)
authenticated encryption ciphers, used mainly for Galois/Counter Mode (GCM) and CCM mode of Advanced Encryption Standard (AES) encryption. TLS Extensions...
178 KB (17,514 words) - 17:10, 3 May 2025
Dynamic Encryption is a cryptographic principle that enables two parties to change the encryption algorithm for every transaction. The principle of Dynamic...
4 KB (358 words) - 05:39, 18 January 2025
BitLocker (redirect from Bitlocker Drive Encryption)
volume encryption feature included with Microsoft Windows versions starting with Windows Vista. It is designed to protect data by providing encryption for...
37 KB (3,534 words) - 03:51, 24 April 2025
In cryptography, the ElGamal encryption system is an asymmetric key encryption algorithm for public-key cryptography which is based on the Diffie–Hellman...
10 KB (1,473 words) - 11:12, 31 March 2025
RSA cryptosystem (redirect from RSA encryption)
That system was declassified in 1997. In a public-key cryptosystem, the encryption key is public and distinct from the decryption key, which is kept secret...
60 KB (7,787 words) - 09:48, 9 April 2025
Email encryption is encryption of email messages to protect the content from being read by entities other than the intended recipients. Email encryption may...
14 KB (1,675 words) - 06:22, 23 April 2025
Link encryption is an approach to communications security that encrypts and decrypts all network traffic at each network routing point (e.g. network switch...
2 KB (205 words) - 07:57, 22 December 2024
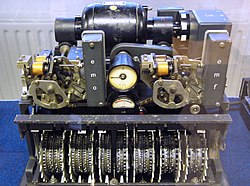
Cryptography prior to the modern age was effectively synonymous with encryption, converting readable information (plaintext) to unintelligible nonsense...
99 KB (10,975 words) - 20:28, 3 April 2025
HTTPS (redirect from HTTPS encryption)
(HTTPS) is an extension of the Hypertext Transfer Protocol (HTTP). It uses encryption for secure communication over a computer network, and is widely used on...
42 KB (4,298 words) - 15:56, 21 April 2025
Disk encryption is a special case of data at rest protection when the storage medium is a sector-addressable device (e.g., a hard disk). This article presents...
30 KB (3,772 words) - 11:25, 5 December 2024
Caesar cipher (redirect from Caesar encryption)
Caesar's code, or Caesar shift, is one of the simplest and most widely known encryption techniques. It is a type of substitution cipher in which each letter in...
19 KB (2,062 words) - 12:24, 29 April 2025
Database encryption can generally be defined as a process that uses an algorithm to transform data stored in a database into "cipher text" that is incomprehensible...
27 KB (3,212 words) - 02:34, 12 March 2025
Identity-based encryption (IBE), is an important primitive of identity-based cryptography. As such it is a type of public-key encryption in which the public...
16 KB (1,942 words) - 00:54, 12 April 2025