Computer security (also cybersecurity, digital security, or information technology (IT) security) is a subdiscipline within the field of information security...
220 KB (22,338 words) - 20:40, 28 April 2025
A security hacker or security researcher is someone who explores methods for breaching defenses and exploiting weaknesses in a computer system or network...
55 KB (5,959 words) - 17:27, 22 January 2025
someone's webmail account, to cracking the security of a bank. The maximum penalty for unauthorized access to a computer is two years in prison and a fine. There...
18 KB (1,870 words) - 11:22, 16 April 2025
13–14. Kakareka, Almantas (2009). "23". In Vacca, John (ed.). Computer and Information Security Handbook. Morgan Kaufmann Publications. Elsevier Inc. p. 393...
26 KB (3,290 words) - 21:09, 28 April 2025
integrity and security of computer systems. Exploits can cause unintended or unanticipated behavior in systems, potentially leading to severe security breaches...
18 KB (1,949 words) - 23:54, 28 April 2025
In computer security, a sandbox is a security mechanism for separating running programs, usually in an effort to mitigate system failures and/or software...
10 KB (1,000 words) - 12:32, 12 November 2024
In computer security, a threat is a potential negative action or event enabled by a vulnerability that results in an unwanted impact to a computer system...
39 KB (4,709 words) - 04:18, 5 May 2025
There are various companies that provide computer security services, develop computer security software or resell software exploits. ADF Solutions Altor...
3 KB (212 words) - 10:25, 20 April 2025
A computer security conference is a convention for individuals involved in computer security. They generally serve as meeting places for system and network...
40 KB (3,962 words) - 22:40, 15 February 2025
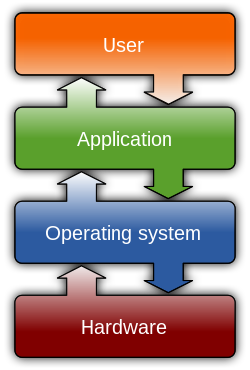
A computer security model is a scheme for specifying and enforcing security policies. A security model may be founded upon a formal model of access rights...
2 KB (184 words) - 14:25, 17 July 2024
Computer security software or cybersecurity software is any computer program designed to influence information security. This is often taken in the context...
9 KB (1,064 words) - 15:27, 31 January 2025
A computer emergency response team (CERT) is an incident response team dedicated to computer security incidents. Other names used to describe CERT include...
31 KB (1,595 words) - 17:07, 21 April 2025
A computer security policy defines the goals and elements of an organization's computer systems. The definition can be highly formal or informal. Security...
3 KB (305 words) - 13:55, 27 January 2025
cryptography and computer security involve studying the means for secure communication and preventing security vulnerabilities. Computer graphics and computational...
72 KB (6,673 words) - 05:26, 18 April 2025
is a security vulnerability in systems that use Diffie–Hellman key exchange with the same prime number. It was discovered by a team of computer scientists...
12 KB (1,297 words) - 06:30, 11 March 2025
A computer virus is a type of malware that, when executed, replicates itself by modifying other computer programs and inserting its own code into those...
92 KB (9,553 words) - 18:54, 4 May 2025
In information security, computer security and network security, an asset is any data, device, or other component of the environment that supports information-related...
3 KB (284 words) - 03:13, 5 May 2025
topical guide to computer security: Computer security (also cybersecurity, digital security, or information technology (IT) security) is a subdiscipline...
49 KB (5,240 words) - 07:50, 31 March 2025
Kevin Mitnick (redirect from Mitnick Security Consulting)
2023) was an American computer security consultant, author, and convicted hacker. In 1995, he was arrested for various computer and communications-related...
39 KB (3,176 words) - 20:15, 4 May 2025
principal in computer security is an entity that can be authenticated by a computer system or network. It is referred to as a security principal in Java...
2 KB (177 words) - 10:17, 25 December 2024
In the computer security or Information security fields, there are a number of tracks a professional can take to demonstrate qualifications. Four sources...
42 KB (634 words) - 01:02, 7 April 2025
information security management scheme. Computer security, IT security, ICT security, and network security are thus all subdomains of information security. National...
25 KB (2,608 words) - 04:03, 9 April 2025
Hacker (redirect from Computer hacking)
associated in popular culture with a security hacker – someone with knowledge of bugs or exploits to break into computer systems and access data which would...
39 KB (4,243 words) - 17:45, 28 March 2025
of computer networks and can circumvent security protocols. They may create malware, a form of software that enables illegitimate access to computer networks...
14 KB (1,671 words) - 14:01, 23 April 2025
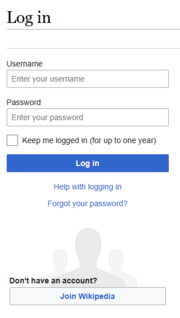
Login (redirect from Logging (computer security))
In computer security, logging in (or logging on, signing in, or signing on) is the process by which an individual gains access to a computer system or...
7 KB (801 words) - 01:59, 24 April 2025
ESET NOD32 (redirect from Eset smart security)
antivirus software Comparison of computer viruses Paul Wilders (24 March 2004). "NOD32 - What does it mean?". Wilders Security Forums. Retrieved 22 November...
21 KB (2,231 words) - 16:23, 24 April 2025
as an information technology security audit or a computer security audit. However, information security encompasses much more than IT. The auditor is responsible...
31 KB (4,030 words) - 09:48, 18 March 2025
fields of computer security and information technology, computer security incident management involves the monitoring and detection of security events on...
12 KB (1,473 words) - 19:34, 9 March 2025
Internet security is a branch of computer security. It encompasses the Internet, browser security, web site security, and network security as it applies...
24 KB (2,640 words) - 11:48, 18 April 2025
The Computer Security Institute (CSI) was a professional membership organization serving practitioners of information, network, and computer-enabled physical...
5 KB (421 words) - 03:54, 21 January 2025