The Metasploit Project is a computer security project that provides information about security vulnerabilities and aids in penetration testing and IDS...
17 KB (1,622 words) - 17:11, 2 June 2025
H. D. Moore (section Metasploit Framework)
programmer, and hacker. He is the founder of the Metasploit Project and was the main developer of the Metasploit Framework, a penetration testing software suite...
9 KB (837 words) - 18:45, 9 March 2025
management tool), Nmap (a port scanner), Wireshark (a packet analyzer), metasploit (penetration testing framework), John the Ripper (a password cracker)...
27 KB (2,220 words) - 23:21, 2 June 2025
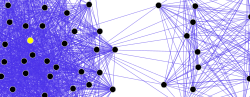
Armitage is a graphical cyber attack management tool for the Metasploit Project that visualizes targets and recommends exploits. It is a free and open...
3 KB (194 words) - 13:34, 14 December 2024
Offensive Security (section Metasploit)
Kali Linux by default, or could be added to other Linux distributions. Metasploit Unleashed is a charity project created by Offensive Security for the sake...
23 KB (1,565 words) - 06:09, 23 April 2025
shellcode. Suitable instructions are often present in large code. The Metasploit Project, for example, maintains a database of suitable opcodes, though...
46 KB (5,132 words) - 08:55, 25 May 2025
OWASP Web Testing Environment (WTW), and Metasploitable. BackBox Hping Metasploit Project Nessus Nmap OWASP ZAP SAINT w3af Burp Suite Wireshark John the...
29 KB (3,516 words) - 21:18, 27 May 2025
these include: Disk and memory forensics DoS attacks Frameworks such as: Metasploit Network Security Reverse engineering Security scanners such as: Burp Suite...
18 KB (1,870 words) - 12:31, 26 May 2025
forks based on Nessus like OpenVAS and Greenbone Sustainable Resilience. Metasploit Project OpenVAS Security Administrator Tool for Analyzing Networks (SATAN)...
3 KB (161 words) - 00:30, 20 May 2025
system, as well as the older Windows versions. On 6 September 2019, a Metasploit exploit of the wormable BlueKeep security vulnerability was announced...
22 KB (1,849 words) - 05:45, 13 May 2025
with the Web Archive format was discovered and reported by Joe Vennix, a Metasploit Project developer. The exploit allows an attacker to send a crafted Web...
7 KB (622 words) - 02:18, 14 March 2025
doi:10.17487/RFC2167. Retrieved 2014-05-27. "Can't Exploit Machines? A Metasploit Troubleshooting How To". Rapid7. June 2012. Retrieved 2020-07-07. Franke...
320 KB (13,096 words) - 14:37, 4 June 2025
Internet suicide pact Legal aspects of computing List of computer criminals Metasploit Project National Crime Agency (NCA) Penetration test Police National E-Crime...
97 KB (9,867 words) - 03:54, 2 June 2025
started working at the security consulting firm Rapid7 that develops Metasploit. Born in December 1970, Mudge graduated from the Berklee College of Music...
39 KB (3,140 words) - 07:45, 13 May 2025
crash and core dump.[citation needed] Code injection Cross-site scripting Metasploit Project OWASP Open Web Application Security Project Prompt injection,...
47 KB (4,983 words) - 10:03, 1 May 2025
Exploit kit Hacking: The Art of Exploitation (second edition) IT risk Metasploit Shellcode w3af Latto, Nica (2020-09-29). "Exploits: What You Need to Know"...
18 KB (1,951 words) - 11:04, 25 May 2025
multi-cultural residents of the asteroid belt. The phrase has been adopted by the Metasploit computer penetration framework as the name of a shellcode encoder. It...
8 KB (931 words) - 11:40, 16 May 2025
Computer security Buffer overflow Exploit (computer security) Heap overflow Metasploit Project Shell (computing) Shell shoveling Stack buffer overflow Vulnerability...
25 KB (2,909 words) - 23:12, 13 February 2025
which was addressed by Microsoft security update MS08-068. For example, Metasploit can be used in many cases to obtain credentials from one machine which...
29 KB (3,408 words) - 17:14, 6 January 2025
authenticated ID IDN homograph attack – Visually similar letters in domain names Metasploit Project – Computer security testing toolPages displaying short descriptions...
13 KB (1,647 words) - 09:07, 22 March 2025
option. BackTrack included many well known security tools including: Metasploit for integration Wi-Fi drivers supporting monitor mode (rfmon mode) and...
15 KB (976 words) - 09:34, 22 May 2025
enough. Cain and Abel Crack Aircrack-ng John the Ripper Hashcat L0phtCrack Metasploit Project Ophcrack Cryptool Brute-force attack E-mail address harvesting...
6 KB (705 words) - 02:46, 25 May 2025
into the Metasploit Project in August 2011. The WarVOX project is no longer maintained. Free and open-source software portal H. D. Moore Metasploit Rapid7...
3 KB (204 words) - 21:35, 15 November 2024
Foundation". The Linux Foundation. 2018-03-19. Retrieved 2018-03-27. "Metasploit: A Penetration Tester's Guide to IPMI and BMCs". Rapid7.com. 2013-07-02...
19 KB (2,226 words) - 17:15, 29 April 2025
also ported at the same event. They were made available as open sourced Metasploit modules. At the end of 2018, millions of systems were still vulnerable...
23 KB (1,902 words) - 16:20, 4 June 2025
file to be executed by the server. Attack (computing) Code injection Metasploit Project, an open-source penetration testing tool that includes tests for...
9 KB (1,036 words) - 20:05, 22 January 2025
portal Aircrack-ng BackBox BackTrack hping Kali Linux Kismet (software) Metasploit Framework Nessus (software) Netcat OpenVAS SAgggl for Analyzing Networks...
24 KB (2,355 words) - 13:07, 27 December 2024
original on May 13, 2010. Retrieved February 5, 2014. Maynor, David (2011). Metasploit Toolkit for Penetration Testing, Exploit Development, and Vulnerability...
14 KB (1,560 words) - 13:58, 18 May 2025
security) Grey hat Groupthink Hacker (computer security) Hacker ethic IT risk Metasploit Murder board Vulnerability (computing) Wireless identity theft Zenko,...
45 KB (5,495 words) - 20:09, 19 May 2025
library libjdwp. It can be activated using the -Xrunjdwp parameter of Java. Metasploit includes a module for JDWP. It can exploit it using various scripts, which...
2 KB (201 words) - 14:56, 19 June 2023