that are 224, 256, 384 or 512 bits: SHA-224, SHA-256, SHA-384, SHA-512, SHA-512/224, SHA-512/256. SHA-256 and SHA-512 are novel hash functions computed... 45 KB (4,583 words) - 15:19, 26 April 2024 |
against SHA-1 are practical. As such, it is recommended to remove SHA-1 from products as soon as possible and instead use SHA-2 or SHA-3. Replacing SHA-1 is... 51 KB (5,763 words) - 18:12, 24 April 2024 |
of the same series of standards, SHA-3 is internally different from the MD5-like structure of SHA-1 and SHA-2. SHA-3 is a subset of the broader cryptographic... 51 KB (5,620 words) - 14:24, 19 April 2024 |
Secure Hash Algorithms (redirect from SHA family) SHA), FIPS PUB 180-1 (SHA-1), FIPS PUB 180-2 (SHA-1, SHA-256, SHA-384, and SHA-512). NIST has updated Draft FIPS Publication 202, SHA-3 Standard separate... 3 KB (464 words) - 03:57, 19 March 2024 |
 | Cryptographic hash function (section SHA-2) Documents may refer to SHA-1 as just "SHA", even though this may conflict with the other Secure Hash Algorithms such as SHA-0, SHA-2, and SHA-3. RIPEMD (RACE... 45 KB (6,067 words) - 11:48, 27 April 2024 |
Charmaine Shamiso Mapimbiro (born 13 July 1994), professionally known as Sha Sha, is a Zimbabwean-born singer-songwriter from Mutare. Hailed by many as... 13 KB (909 words) - 20:31, 27 March 2024 |
NIST hash function competition (redirect from SHA-3 competition) function called SHA-3 to complement the older SHA-1 and SHA-2. The competition was formally announced in the Federal Register on November 2, 2007. "NIST... 27 KB (2,244 words) - 20:34, 28 February 2024 |
 | HMAC (redirect from HMAC-SHA-256) key prior to communication. Any cryptographic hash function, such as SHA-2 or SHA-3, may be used in the calculation of an HMAC; the resulting MAC algorithm... 19 KB (2,305 words) - 16:54, 4 April 2024 |
Simple Network Management Protocol (section Version 2) (Proposed|Historic) — HMAC-SHA-2 Authentication Protocols in the User-based Security Model (USM) for SNMPv3 RFC 7860 (Proposed) — HMAC-SHA-2 Authentication Protocols... 40 KB (5,033 words) - 11:22, 11 April 2024 |
MD5, SHA-1 and most of SHA-2 that are based on the Merkle–Damgård construction are susceptible to this kind of attack. Truncated versions of SHA-2, including... 7 KB (1,034 words) - 09:54, 23 April 2024 |
block, XORed with round constants, is added before each ChaCha round. Like SHA-2, there are two variants differing in the word size. ChaCha operates on a... 30 KB (2,814 words) - 09:48, 25 April 2024 |
Windows Server 2008 (redirect from Windows Server 2008 Service Pack 2) Windows updates with the SHA-2 algorithm. As a result of this Microsoft released several updates throughout 2019 to add SHA-2 signing support to Windows... 52 KB (4,823 words) - 01:46, 3 May 2024 |
for further use", and most U.S. government applications now require the SHA-2 family of hash functions. In 2012, the Flame malware exploited the weaknesses... 41 KB (4,405 words) - 16:27, 16 March 2024 |
Shas (Hebrew: ש״ס) is a Haredi religious political party in Israel. Founded in 1984 under the leadership of Rabbi Ovadia Yosef, a former Israeli Sephardi... 38 KB (3,046 words) - 06:08, 1 May 2024 |
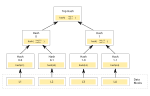 | child nodes under each node. Usually, a cryptographic hash function such as SHA-2 is used for the hashing. If the hash tree only needs to protect against... 15 KB (1,787 words) - 22:42, 29 April 2024 |
 | Tsim Sha Tsui (Chinese: 尖沙嘴; pinyin: Jīmsājéui), often abbreviated as TST, is an urban area in southern Kowloon, Hong Kong. The area is administratively... 25 KB (2,865 words) - 15:53, 29 April 2024 |
 | Kong. Administratively, it is part of the Sha Tin District. Sha Tin is one of the neighbourhoods of the Sha Tin New Town project. The new town was founded... 26 KB (2,390 words) - 04:24, 5 April 2024 |
e={\textrm {HASH}}(m)} . (Here HASH is a cryptographic hash function, such as SHA-2, with the output converted to an integer.) Let z {\displaystyle z} be the... 19 KB (2,822 words) - 03:20, 30 April 2024 |
Chalim Perry (born April 8, 2003), known by his stage name Sha EK (Sha Everybody Killer), is an American rapper and producer from The Bronx, New York... 7 KB (420 words) - 03:22, 17 April 2024 |
 | Sha Na Na was an American rock and roll and doo-wop revival group formed in 1969. The group performed a song-and-dance repertoire based on 1950s hit songs... 35 KB (3,875 words) - 13:22, 3 May 2024 |
sha512sum, which use a specific SHA-2 hash function and b2sum, which uses the BLAKE2 cryptographic hash function. The SHA-1 variants are proven vulnerable... 6 KB (577 words) - 11:01, 27 September 2023 |
Dogrel (redirect from Sha Sha Sha) 9) Tom Coll – drums (1–11), tambourine (8, 10), miscellaneous percussion (2) Conor Deegan – bass guitar (1–11), piano (4), baritone guitar (5), surf guitar... 14 KB (1,047 words) - 07:02, 3 February 2024 |
Sha Sha is the debut album by American indie rock singer, songwriter, multi-instrumentalist and former Radish member Ben Kweller. The album was originally... 7 KB (511 words) - 20:04, 29 March 2024 |
('md5crypt') $2$: Blowfish-based crypt ('bcrypt') $sha1$: SHA-1-based crypt ('sha1crypt') $5$: SHA-256-based crypt ('sha256crypt') $6$: SHA-512-based crypt... 26 KB (2,749 words) - 08:20, 20 April 2024 |
Symantec. Archived from the original on 2015-12-31. Retrieved 2014-07-28. "SHA-256 Compatibility". Archived from the original on 2015-07-01. Retrieved 2015-06-12... 118 KB (3,316 words) - 19:39, 18 April 2024 |
attacker to find two messages X and Y such that SHA(X) = SHA(Y), even though anyone may compute SHA(X). SipHash instead guarantees that, having seen... 13 KB (1,298 words) - 11:54, 3 May 2024 |
Secure Shell (section Version 2) SHA-256 Algorithm with RSA, Digital Signature Algorithm (DSA), and Elliptic Curve DSA (ECDSA) in SSHFP Resource Records (April 2012) RFC 6668 – SHA-2... 38 KB (4,271 words) - 23:44, 27 April 2024 |
 | result is necessary. While RIPEMD functions are less popular than SHA-1 and SHA-2, they are used, among others, in Bitcoin and other cryptocurrencies... 8 KB (818 words) - 10:16, 29 April 2024 |


